Disclosure: The views and opinions expressed right here belong solely to the creator and don’t symbolize the views and opinions of crypto.information’ editorial.
Because the scandal continues to unfold and consultants look at simply how severely high officers have compromised US nationwide safety in that Sign chat leak—and embarrassed themselves by means of controversial post-statements—I need to take a more in-depth take a look at one specific episode from the story.
You may also like: As AI rewrites historical past, blockchain expertise is a line of protection | Opinion
At first, the White Home denied that the chat ever existed. However when it turned clear that there was an excessive amount of proof to refute, they shifted ways, denying that the chat ever contained any categorised data of nationwide safety significance. And certainly, what proof can journalist Jeffrey Goldberg current after leaving that chat? Furthermore, the chat was set to self-destruct messages after a time period. So think about a court docket listening to the place events are required to current proof, and the one obtainable proof consists of screenshots—in different phrases, just about nothing, as such proof is nearly unimaginable to confirm.
The reply is quite easy—if the journalist had taken care to correctly protect such proof. He might show that he had entry to delicate data at a time when he shouldn’t have, by publishing cryptographic hash sums of that data. Had he not been within the chat, he wouldn’t have recognized when and the place they have been planning to strike Yemen, who the goal was, and so forth. Sure particulars could turn out to be public later, however not on the time the chat occurred—right?
The answer lies in a cryptographic technique often called proof of existence with out disclosure. It includes two primary components: cryptographic hashes and dependable timestamps. This may be executed on blockchain manually—if one is aware of the method—or by means of a wide range of purposes and companies providing blockchain-based timestamping proofs.
Right here’s the way it works: you write a message (for instance, by copying and pasting from the chat), generate a hash sum of the message, publish it on a blockchain, and save the personal key for the handle used to publish it. You’ll later want this personal key to show that it was your handle (i.e., you personally) that printed the hash, and thus that you simply had data of the unique message at the moment. A social media account may additionally serve the same perform, however do not forget that social platforms are centralised methods—weak and, not like blockchains, not immutable.
So, there it’s—a word for all journalists who could someday have to show the existence of a truth with out revealing its contents.
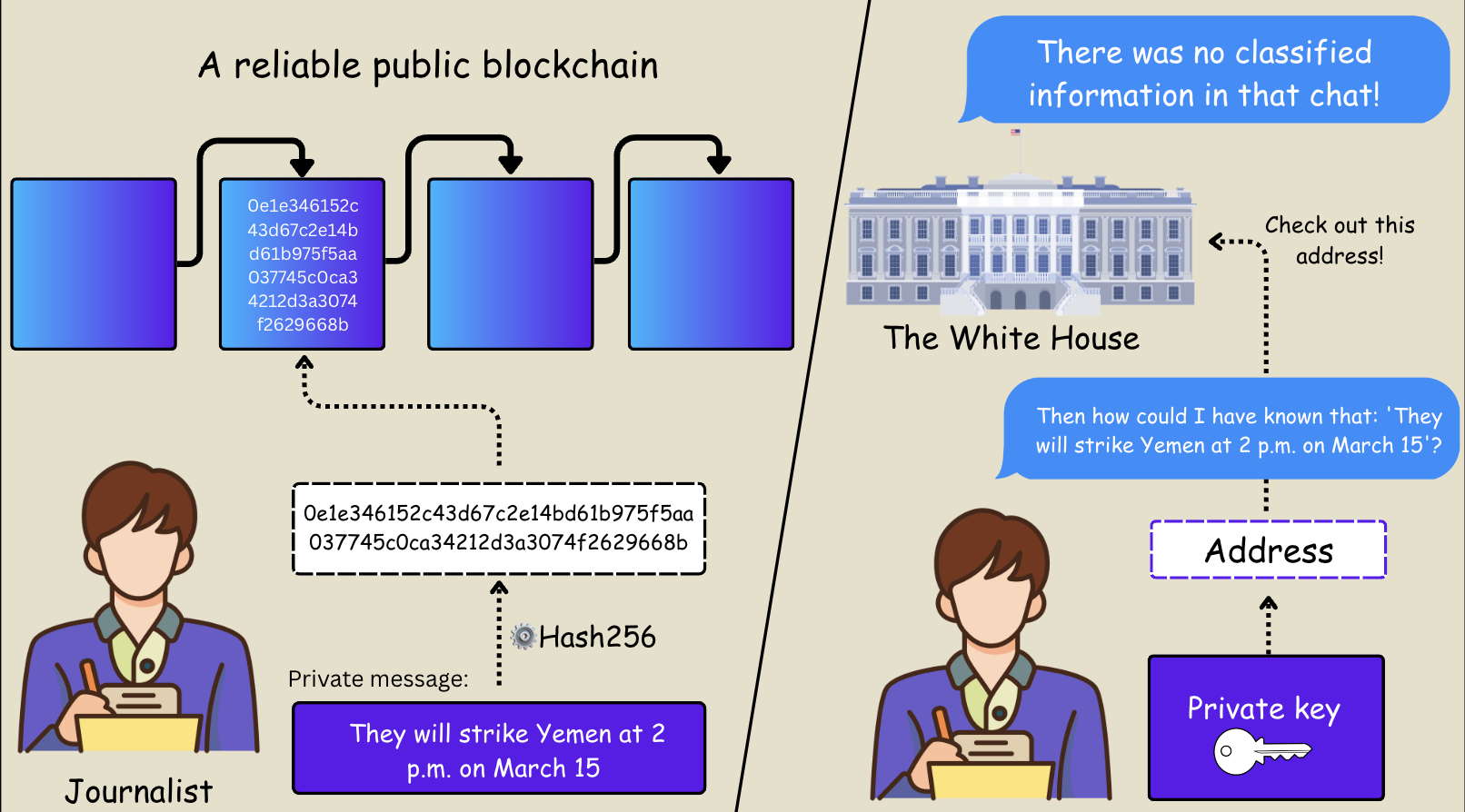
Course of diagram: Proof of existence utilizing blockchain | Supply: Courtesy of the creator
This course of creates an plain, timestamped document confirming {that a} particular authentic message existed and was recognized to the writer on the time the blockchain transaction was confirmed—all with out revealing the content material publicly till the journalist chooses to take action.
Learn extra: Past consensus: Transaction privateness is blockchain’s subsequent safety frontier | Opinion









